PrivacyAnalyzer by SME Lamda Networks www.lamdanetworks.com offers the functionality for aiding the 5G/IoT integrators to assess the privacy strength of their applications or services against confidential information disclosure before they can release their solutions to their clients.
To achieve the above goal, PrivacyAnalyzer receives testing sessions’ traffic stemming from the devices (UEs, IoT devices, etc.) participating in the integrator’s test sessions. Then, PrivacyAnalyzer scans the sessions’ message contents for privacy-sensitive content and reports the outcomes of the analysis to the end-user (integrator) with the goal to enable the end-user to resolve the privacy issues detected in the test sessions before releasing her application or service to her client, typically a network/service operator or an IoT service provider. The software was initially developed as an extend open call project with the F-INTEROP project https://www.f-interop.eu/ via a collaboration between Lamda Networks and Kings College London’s Computer Science group specializing in anonymisation techniques.
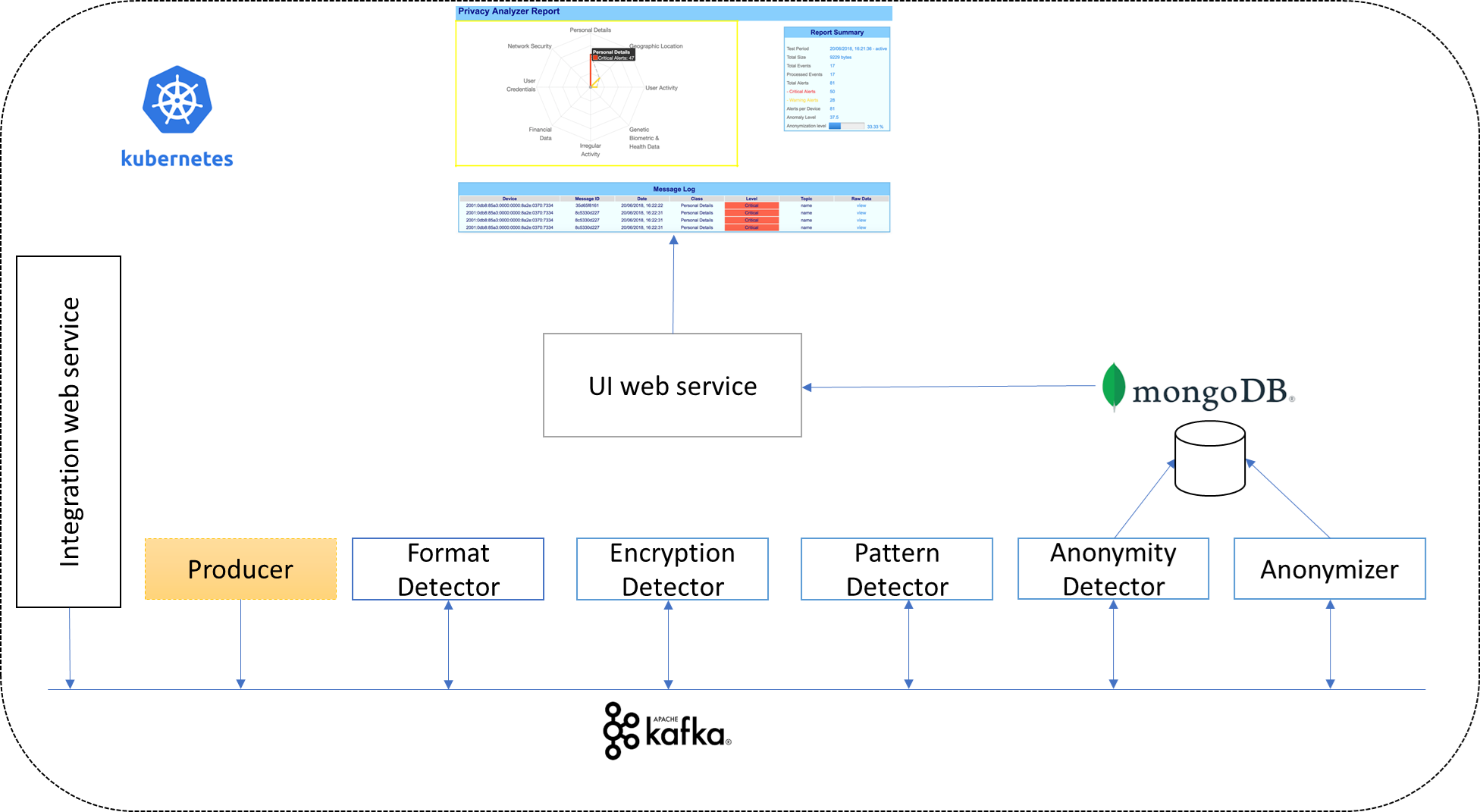
Afterwards, the proof of concept of the software has been highly refactored by investing its own resources so that PrivacyAnalyzer operates as a Software as a Service (SaaS) handling large volumes of incoming messages for different devices. To that end, the Kubernetes framework has been used, together with a cluster running Kafka and a second cluster running mongoDB. The high-level architecture of the cloud version of PrivacyAnalyzer is depicted below. Note that the SaaS can run in the client’s own cloud as well as we support running the SaaS in Google’s and Amazon’s cloud platforms and last, we allow the use of PrivacyAnalyzer to subscribed tenants to our private cloud, the latter being charged via a volume-based subscription fee.
PrivacyAnalyzer has the potential to become an important service in both 5GASP’s use cases as well as a service that could serve other verticals apart from Automotive and PPDR. For the latter verticals, the PrivacyAnalyzer Network Application shall cater for detecting the privacy vulnerability of relevant network devices, which are involved in automotive and/or PPDR communications. As an example, our service might enhance the physical protection of the personnel of the involved authorities (e.g. First Responders) in PPDR operations and overall help the success of ongoing disaster recovery operations.
The current status of the ‘Network Application-ization’ of PrivacyAnalyzer is that we have created the NS and VNF descriptor for OSM 10. Furthermore, we have defined the Helm chart so that our Network Application is able to be onboarded to a 5GASP testbed. We have successfully onboarded to the Patras testbed, using the Patras Harbor repo for uploading our Helm chart whilst the project-wide Helm repo is being established in the consortium with the purpose that each Network Application developer is a tenant, isolated from others, and is able to upload her Docker images and Helm charts in a private space within Harbor.
As the next steps, we are continuing to work within the scope of WP4 and WP5. Our mode term goal is that until summer 2022, PrivacyAnalyzer is deployed (onboarded and instantiated) in three target testbeds (Patras, ININ, Bristol) in order to cater for used for the different usage scenarios of the Network Application as we have defined them within the scope of WP4. Below follows a summary of the roadmap for deployment on the three target testbeds.
In Q1 2022, PrivacyAnalyzer shall be onboarded and instantiated on the Patras, ININ and Bristol testbeds using OSM 10 and their associated K8S VIMs.
In Q2 2022, PrivacyAnalyzer -which we become by then a fully-fledged 5GASP Network Application – shall be deployed on Patras’s, ININ’s and Bristol’s testbeds; the first two addressing the cross-vertical and PPDR use cases respectively and the latter employed for co-working with Bristol’s MEC offloading Network Application.
For any question regarding PrivacyAnalyzer and its transformation to Network Application, please email privacyanalyzer@lamdanetworks.io.